Team Wabbi
October 7, 2022
In a perfect development world, security is an integral part of the process and is integrated into the complete software development cycle. With practicing this approach, development teams implement security protocols and have a clear understanding of policies and workflows.
How does security become embedded into the software development process? Two words: Policy and Workflow.
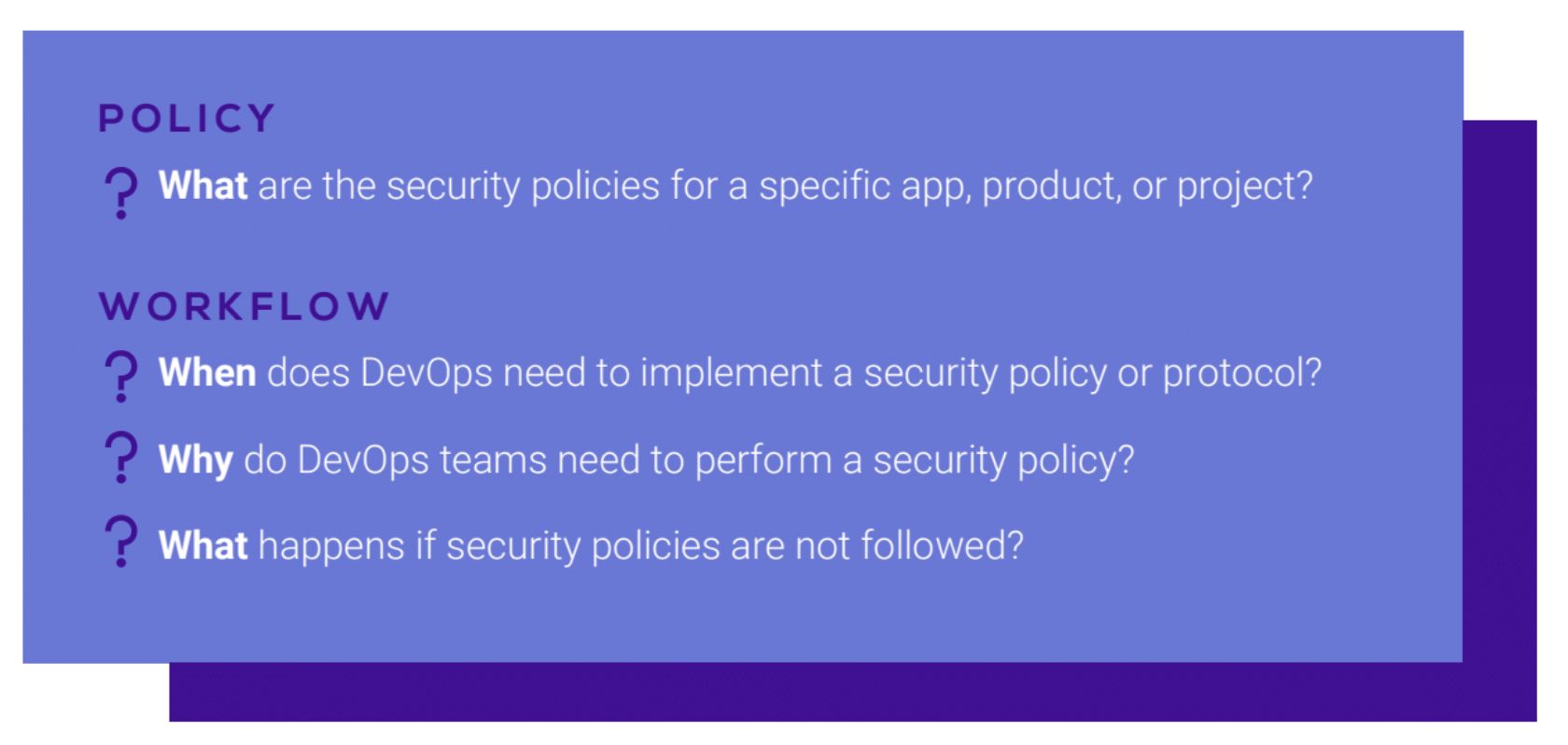
Let’s dive into policy. There are three key components to policy; access, project specific, and address both the security risk and business risk.
Access – Security policies must be accessible to developers whether that means living in an IDE or JIRA ticket. Security policies are not something that should be added to your 53 page development handbook, rather somewhere where they are quickly and easily accessible.
Project Specific – This one is pretty simple. In other words, this means policies should be dynamic and will differ by application or within an application.
Security and Business Risk – Policies really need to address all aspects of risk so DevOps team can have a better understanding that a security breach isn’t just a breach, but rather can expose the organization to serious business risks that can affect financial and personal information.
Now let’s talk about workflows. In an ideal world security policies are always dynamic, attached to a workflow, and mapped to a process. So if a policy is not followed an automated workflow will serve as the solution to continuously ensure security integrations. Workflows must always be fluid. They can be proactive or reactive.
Creating the ideal security process integration in terms of workflow boils down to workflow automation. Often times there are too many static security tools being used and don’t kick off a set of actions. Ideally security policies are attached to a workflow, mapped to a process, and are always dynamic.
What happens if a policy is not followed? An established automated workflow will be the catch to achieve continuous security integration. How does that work? Great question. An automated security workflow will kick off when a security step is skipped and notify the team.
Whether a policy is skipped or followed, automated workflows in place will continuously and dynamically manage security requirements ensuring security remains a top priority for your organization. What is boils down to is a process-oriented continuous security approach – and that is what Wabbi does.
Want to learn more about you can automate AppSec Policies and Controls in your SDLC?
Read our whitepaper on Application Security Orchestration & Correlation (ASOC) here!
Related Articles
December DevSecOps Roundup: Trends Steering the Future of AppSec
Hey! We’re back with the latest in DevSecOps, security by design, and everything in between. Grab your coffee ☕, and let’s dive in! 📌 Top Blogs 🟣 Zero Trust in AppSec: Why It Belongs in Your Pipelines, Too Zero Trust doesn’t end at the firewall. It belongs in your...

Remote Work Cybersecurity Risks (And How To Reduce Them) – Forbes –
This article originally appeared on Forbes on December 15, 2025 Expert Panel® Forbes Councils Member Forbes Technology Council COUNCIL POST| Membership (Fee-Based) getty Remote and hybrid work have opened the door to greater flexibility, stronger talent pipelines and...

Remote Work Cybersecurity Risks (And How To Reduce Them) – Forbes –
This article originally appeared on Forbes on December 15, 2025 Expert Panel® Forbes Councils Member Forbes Technology Council COUNCIL POST| Membership (Fee-Based) getty Remote and hybrid work have opened the door to greater flexibility, stronger talent pipelines and...