Team Wabbi
September 27, 2023
What is Vulnerability Management?
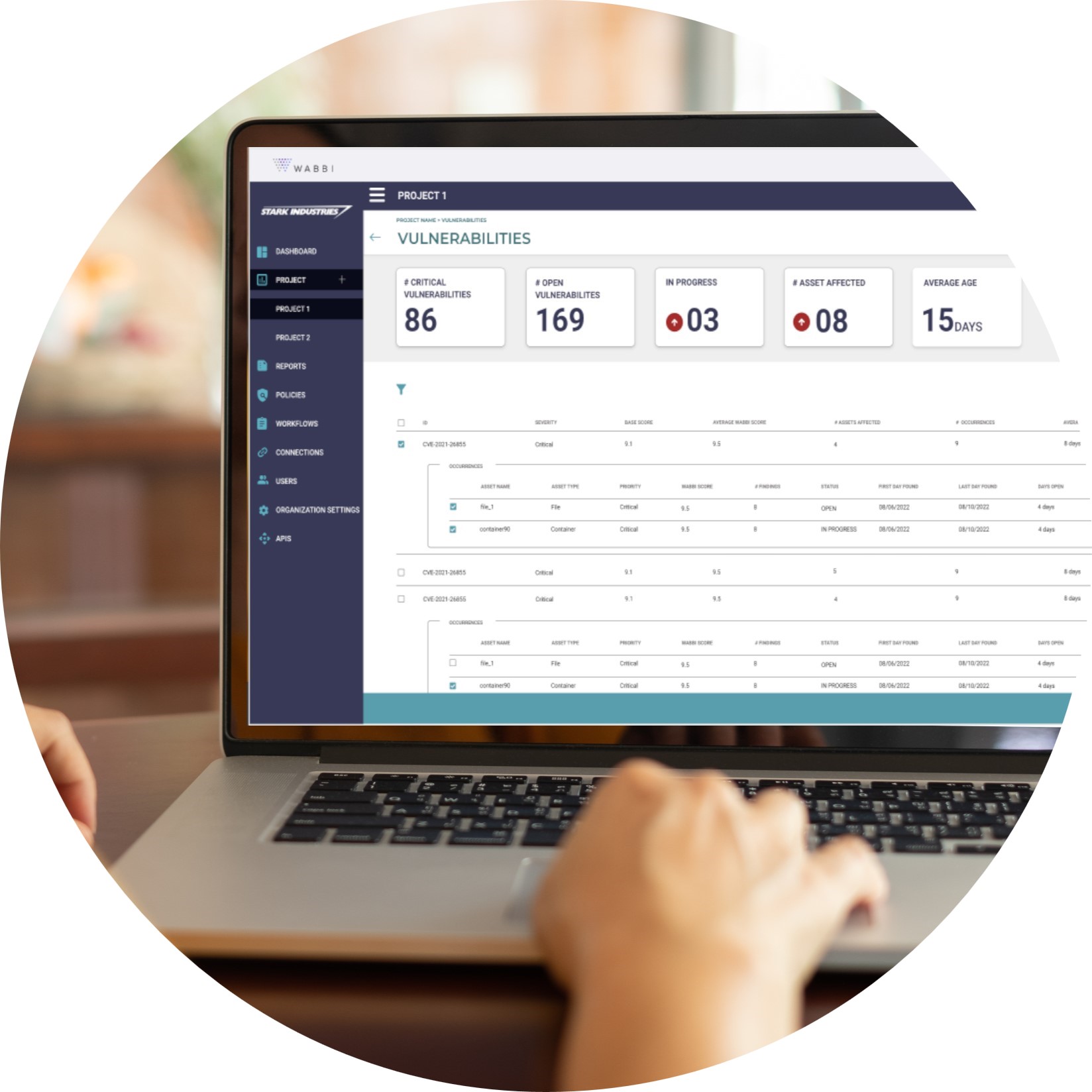
Vulnerability management is the traditional core of an Application Security strategy. It is not just enough to scan, you have to aggregate and prioritize the results. As 2/3 of organizations use at least 11-20 application security tools, with a third of those using 21-50, without vulnerability management, the data generated by application security testing (AST) tools becomes a big problem, fast. By identifying, prioritizing, and remediating security issues with vulnerability management before they become a problem – be it a breach or a bottleneck – organizations can improve the efficacy of their application security tools. But it takes more than just a list of identified vulnerabilities to create a successful vulnerability management program.
Vulnerability management involves managing the list of results from AST to identify weaknesses within a system that could be exploited. Once security issues are identified, they can then be classified according to severity and prioritized for remediation. With multiple scanners, pen tests or other security tools identifying vulnerabilities some refer to the ability to manage all results in a single tool or platform as unified vulnerability management (UVM) to distinguish between the VM solutions of each individual tool and a centralized repository, however we’d argue you’re not doing vulnerability management if you don’t have at least a centralized repository.
Fundamentals of Vulnerability Management
Good vulnerability management requires up-to-date knowledge about emerging threats as well as a comprehensive understanding of how those threats interact with existing systems and networks – both internally and externally. This is where regular scanning of applications and remediation prioritization is critical.
By adopting a proactive approach to vulnerability management – such as implementing automated scanning tools – organizations can ensure that any identified weaknesses are addressed quickly before they become an issue or lead to a breach of security. Additionally, effective vulnerability management will help organizations prioritize which fixes need immediate attention while also reducing noise in their SDLC which ultimately leads to better alignment with their overall risk strategy.
However, the most critical element of vulnerability management is establishing a process that is tailored to the specific needs of the organization. This includes understanding the current risk landscape, determining which assets need protection, categorizing assets based on their sensitivity levels, and assessing the existing security controls in place. Additionally, organizations should consider creating policies and procedures that provide guidance for managing vulnerabilities throughout their software development lifecycles.
In other words, an organization should be able to evaluate their vulnerabilities through three questions:
- What has to be fixed now?
- What can be fixed later?
- What might be fixed in the future?
Once a baseline understanding of the environment has been established, organizations can begin to prioritize identified vulnerabilities according to their level of risk exposure. A comprehensive vulnerability management program goes a step further by integrating additional information such as external threat intelligence feeds and internal threat intelligence generated by monitoring systems to identify those threats with higher priority levels. This allows organizations to focus on remediating those issues with the greatest potential for damage first while also ensuring that risks from lower-priority issues are still monitored and managed properly over time.
Scaling Vulnerability Management
As threats become more sophisticated and the number of identified vulnerabilities grow, it can be difficult to keep up with the process of identifying, prioritizing, and remediating them. To stay ahead of potential bottlenecks and threats, to support vulnerability management at scale – which could mean even as few as 2 AST tools – automated closed feedback loops are table stakes for any VM solution.
This includes integrations to ensure:
- Vulnerability information is updated in real time from AST tools
- Consolidation across time and tools
- DevOps ticketing systems to monitor remediation
Furthermore, it requires collaboration among multiple stakeholders including security teams, business users, operations, development, and IT. This is a two-way street as vulnerability management provides a mechanism to break down silos and provide transparency into the prioritization and remediation process. And when best-in-class it does this without adding noise to existing workflows – just information.
Related Articles
November DevSecOps Roundup: Ideas Shaping What’s Next
Hey! We’re back with the latest in DevSecOps, security by design, and everything in between. Grab your coffee ☕, and let’s dive in! 📌 Top Blogs 🟣 AI is Solving the Puzzle. Are You Missing the Corner Pieces? AI is rewriting the rules of cybersecurity—and attackers...

DevSecOps in Digital Transformation
Click below to listen to this episode of Digital Shifts aka Corporate Evolution Tales, where host Mariam sits down with Brittany Greenfield, founder and CEO of Wabbi, to discuss how to align security with business goals, and why transformation is a continuous...

Zero Trust in AppSec: Why It Belongs in Your Pipelines, Too
Zero Trust in AppSec: Why It Belongs in Your Pipelines, Too Zero Trust has become a cornerstone of modern cybersecurity strategies. The principle is simple but powerful: “never trust, always verify.” Traditionally, Zero Trust has been applied at the network and access...

How Tech Companies Can Break Out Of Innovation Stagnation – Forbes –
This article originally appeared on Forbes on November 5, 2025 Expert Panel® Forbes Councils Member Forbes Technology Council COUNCIL POST| Membership (Fee-Based) getty For tech companies, early success can be both a gift and a trap. The same products and systems that...
Wabbi Named a “Vendor to Watch” in IDC MarketScape: Application Security Posture Management (ASPM) 2025 Vendor Assessment
BOSTON / Press Release / September 18, 2025 Wabbi, a leader in Application Security Posture Management, is proud to announce that it has been named as a Vendor to Watch in the IDC MarketScape: Application Security Posture Management (ASPM) 2025 Vendor Assessment. This...