Team Wabbi
July 3, 2024
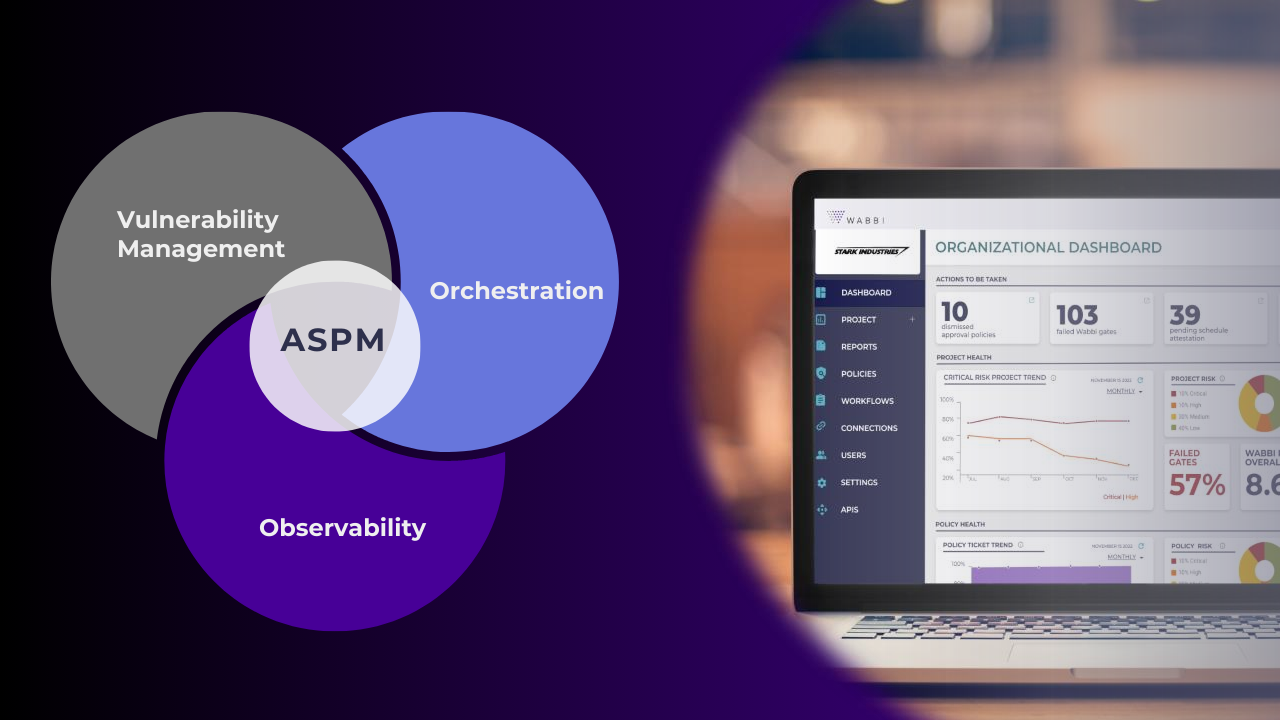
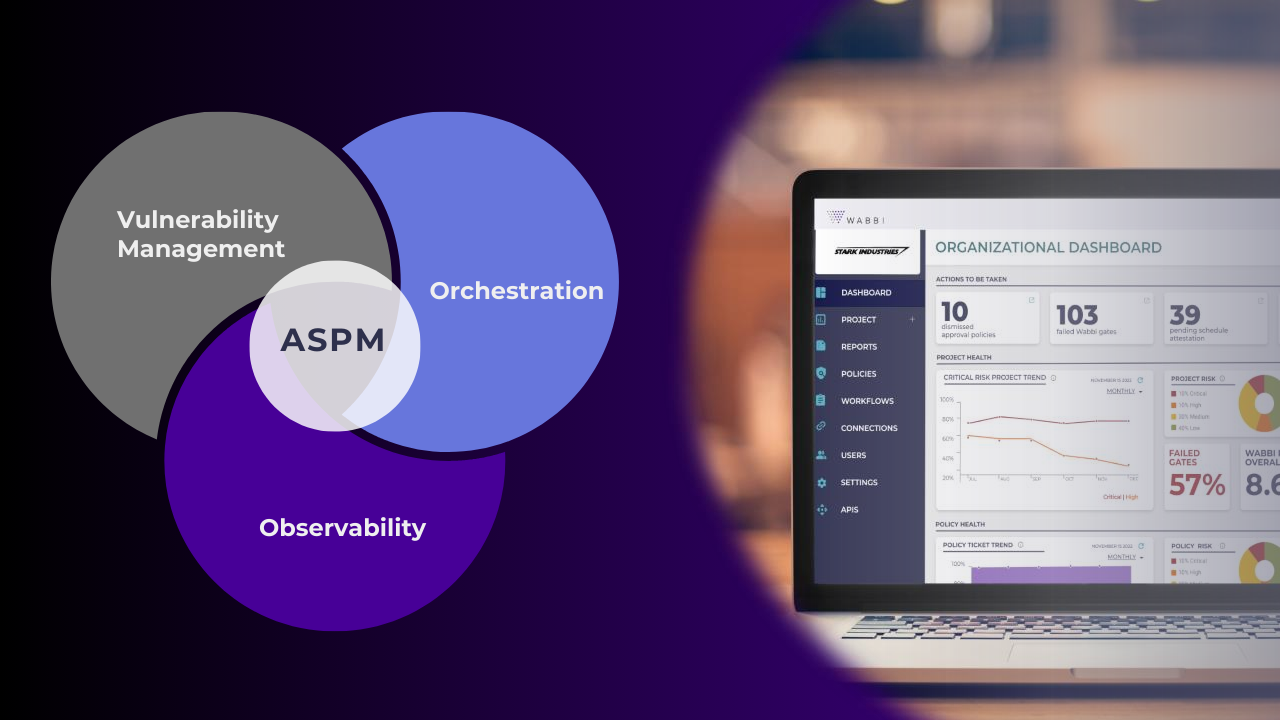
As the importance of Application Security has grown, so has the confusion around how to successfully maintain the complete application security lifecycle– not to mention stay up to date with the alphabet soup of acronyms we must contend with. Consequently, as organizations establish their application security posture management (ASPM) strategies, it can be easy to gravitate to point solutions that tout the familiar, like vulnerability management, orchestration and observability, and while all these components are critical to an application security posture management strategy, without all the pieces of the puzzle in lock together, organizations are left with holes in building cyber-resilience.
So, let’s break down the pieces, debunk the myths of why individually they’ll deliver better application security posture, and understand how together as part of an ASPM solution they can manage the end-to-end application security lifecycle as an integrated part of the SDLC.
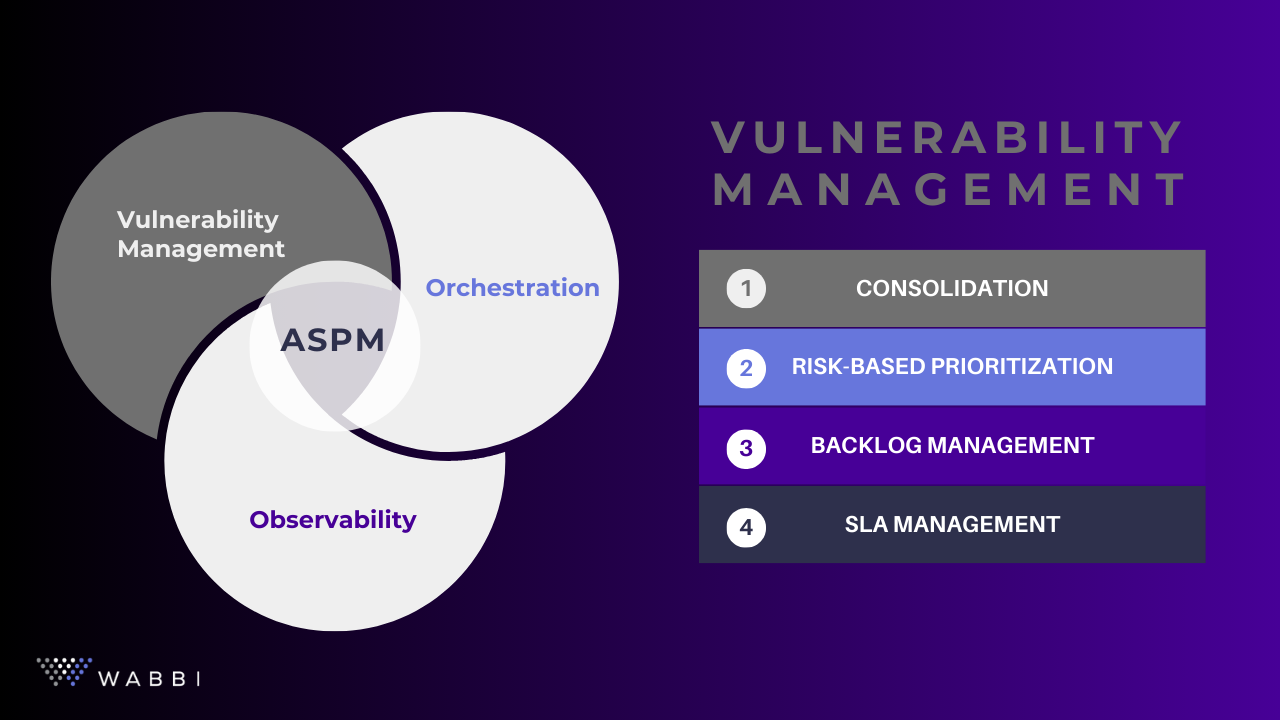
Vulnerability Management
In today’s cybersecurity landscape, vulnerability management is a critical component of protecting digital assets from potential breaches. This is the bread and butter of any application security program, allowing organizations to aggregate and prioritize, and track remediation of vulnerabilities.
However, even the best-in-class vulnerability management solution is limited as it only tackles one part of the full application security lifecycle. To be effective, vulnerabilities need to be viewed in the context of risk and as part of an integrated security program. The context that ties security components together enables organizations to build a more adaptive and unified defense against persistent threats.
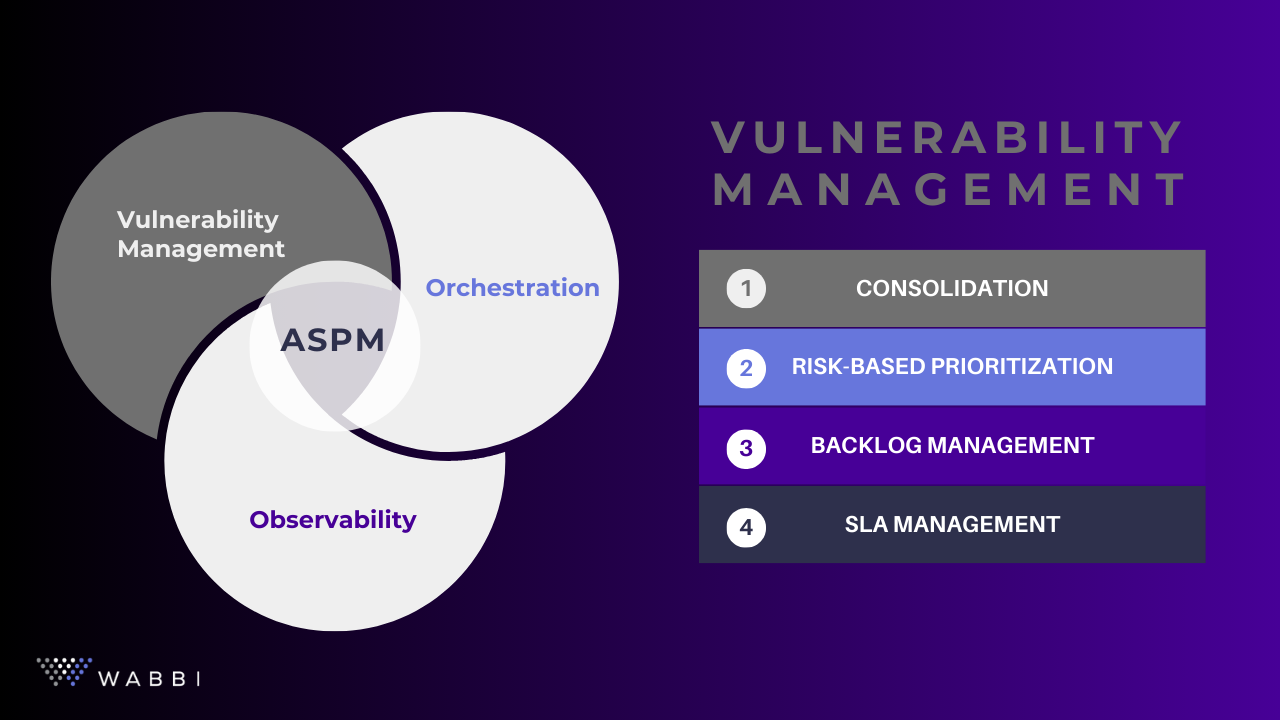
Simply put, standalone vulnerability management is just better list management – helpful, but myopic and limited in its ability to significantly move the needle in improving an overall application security posture. Even with the rise of risk-based vulnerability management (RBVM) which enables better alignment of risk and remediation prioritization, vulnerability management remains siloed without dynamic workflows that can respond to changes in application and security requirements, as well as create inflection points within the SDLC.

Orchestration
Orchestration is an extension of automation that moves beyond the use of technology to complete individual tasks or processes that are repetitive and time-consuming – such as starting a security scan – by taking a process focus, focusing on entire workflows or processes, involving multiple automated tasks that need to be coordinated to allow for end-to-end administration of all tasks that comprise a workflow, ensuring all parts of a process are executed in the correct order.
For those that rely on a single vendor for their application security program, the integrated orchestration between the existing product suite may satisfy their needs, however, the nuance of application security strategies means most organizations are looking for a universal platform that can easily plug-and-play tools from different vendors into these workflows as they evolve their application security program. A methodology and tool agnostic approach.
With 100 developers for every 1 application security manager, orchestration is essential to ensure security can keep pace with development and not become a bottleneck. However, without SDLC awareness or risk-management metrics, orchestration tools ineffectively contextualize security components.
Observability
The concept of observability is better known as “a single pane of glass.” And like in DevOps, observability and monitoring are related but distinct concepts, where monitoring focuses on the process of collecting and analyzing predefined sets of metrics, logs, and traces to ensure the system is functioning as expected and to detect anomalies, outages, and performance issues, and will deliver alerts for specific events or thresholds.
Observability is a broader concept that refers to the ability to infer the internal state of a system based on its outputs. It involves collecting and correlating a wide range of data to provide a holistic view of the system’s health and performance. The main goal of observability is to understand why something is happening within the system, not just what is happening. It allows for more proactive and deep insights. It emphasizes the correlation of different types of data to provide context and a deeper understanding of issues.

However, as a standalone, application security observability tools may provide insights, but it fails to be able to actively manage the application security lifecycle as a dynamic part of the SDLC.
Application Security Posture Management (ASPM)
It may sound obvious, but the key here is the word management. To actually effectively integrate security into the SDLC, it is not enough to have just aggregation (vulnerability management), just speed (orchestration), or just insights (observability), but all these insights must be turned into not just information, but actionable information. This is where organizations have the ability to get control and consistency of managing their application security posture.
It is the trifecta of the three components – vulnerability management, orchestration, & observability that comprises an ASPM platform. However, with ASPM being named one of Gartner’s transformational technologies in Application Security, Cybersecurity & IT Intelligence Management, platforms have been eager to adopt this moniker for their platforms even without having the full trifecta.
While there’s no doubt the goal of all ASPM providers remains the same to offer a comprehensive view and control of security across applications and infrastructure, empowering organizations to manage their security risk in tandem with their business objectives, most platforms have failed to bring together these pillars to integrate, orchestrate, and manage the end-to-end lifecycle of an application security program.


Conclusion
This fragmentation leaves organizations contending with a complex and disjointed application security landscape, making it hard to start advancing their application security program to meet and marry with the needs of today’s development organization. And even worse, the selection of a point solution instead of a comprehensive ASPM platform can quickly derail their DevSecOps transformation as they are left with an incomplete picture of their posture and no ability to consistently manage it. This is not to say that organizations can’t start their transformation with just one of these components, however they must pick a solution – not a tool – that will grow with them.
So, if you remember nothing else, remember the pieces of the puzzle are:
- Vulnerability Management which organizes data
- Orchestration which puts that data into workflows; and
- Observability which makes that data insightful,
but only Application Security Posture Management is the complete puzzle, pulling together all three so that security can be seamlessly integrated into development to enable organizations to manage cyber risk as an integral part of their business objectives, aligning security efforts with overall business goals.
Related Articles

Begin Your Security Integration Into DevOps Today
You can argue that SecDevOps is an approach as old as time - or rather, DevOps – after all, it was Security that was the instigator of the problems in the Phoenix Project. However, it has come into focus in the last 5 years as 17% of companies had fully embraced...

Accelerating Vulnerability Management through SecDevOps
Vulnerabilities are all around us. This has always been the case, but since the novel coronavirus (COVID-19) led to massive global changes, small vulnerabilities have led to major disruptions in businesses of all sizes - a problem that won’t disappear anytime soon:...

Remote Work: The Breakthrough Moment for SecDevOps
While SecDevOps – the integration of Security into Development processes - has grown in prominence as an extension of the broader DevSecOps movement, despite recognizing the use of better integrated and automated application security as a top 3 priority, companies...

Wabbi Statement on Recent Events
Like many people, my start of June 2020 has been filled with much conversation surrounding the protests around the country and the world in the wake of the death of George Floyd. As I believe we cannot fully understand and move forward until we take the time to absorb...
No Results Found
The page you requested could not be found. Try refining your search, or use the navigation above to locate the post.